When implementing support for TLS1.2 and client-server certificate verification for MyNatsClient I needed a quick way to generate: CA, Server and Client certificates. I could of course script this and use OpenSSL but I found a small and simple docker image that simplified this process. Lets have a quick look of how to accomplish this.
NOTE! I've done this only for TESTING purposes.
The Image
The docker image I've chosen to use is: OMGWTFSSL It has a lot of different switches you can use. I'll use a few of them when generating the certificates below.
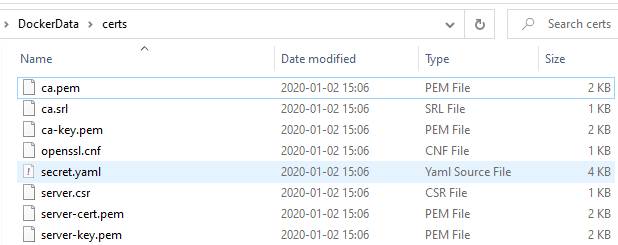
Step 1 - Generate certs for CA and Server
docker run --name servercerts
-v //E/DockerData/certs/:/certs
-e CA_EXPIRE=365
-e SSL_EXPIRE=365
-e SSL_KEY=server-key.pem
-e SSL_CERT=server-cert.pem
-e SSL_CSR=server.csr
-e SSL_SUBJECT=localhost
paulczar/omgwtfssl
As I wanted the certificates on my host machine for inclusion in my GitHub repository (again, they are for TESTING only) I mapped up my local folder: E:\DockerData\certs\ against the image's certs folder
I'm running Docker Desktop Community on Windows and have shared my drive E:\ so that I can map it up.
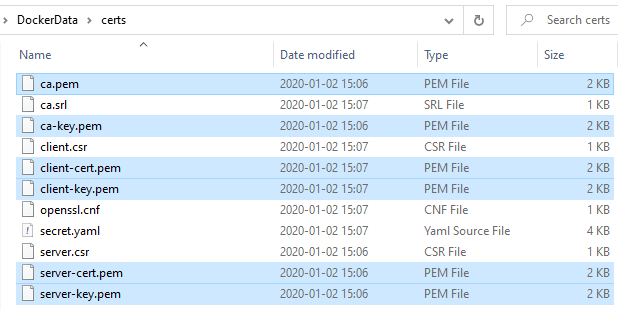
Step 2 - Generate certs for Client
docker run --name clientcerts
-v //E/DockerData/certs/:/certs
-e CA_EXPIRE=365
-e SSL_EXPIRE=365
-e SSL_KEY=client-key.pem
-e SSL_CERT=client-cert.pem
-e SSL_CSR=client.csr
-e SSL_SUBJECT=localhost
paulczar/omgwtfssl
One important thing here is that we run it at the same mapped host directory which still contains the CA certificate. Otherwise the Docker image will not pick that up and the certificates will not be generated with the same CA as a root certificate.
That's it. I now had all the certificates I needed to setup a test environment with a secured NATS-server and a verifying MyNatsClient using TLS1.2. Worked well and solved an issue for me.
Cheers,
//Daniel
